Protecting World Water Supplies Against Backflow Attacks
Water supply networks are susceptible to malicious attacks if not controlled correctly. Dan Kroll explains why countries such as Singapore, Canada and China are taking advantage of multi–parameter monitoring to detect terrorist activities and prevent accidental contamination.
Imagine that you were offered the job of guarding a bank. Now, imagine that on your first day on the job your boss handed you a blindfold and said that you were required to wear it while on duty but would be allowed to take a peek at 10:30 and 2:30 for a couple of minutes each day. You would not be a very effective guard. Yet blindfolded, for the majority of the working day, is in effect how we attempt to secure our water supplies from intentional or accidental contamination.
Other than the snapshot offered by occasional grab samples, little information is available to operators of water distribution systems and the water quality in the pipes once it leaves the treatment plant, essentially leaving them blind to conditions in the distribution system.
In the past, most of our analytical muscle was brought to bear at the treatment plant. Little consideration was given to source waters or the distribution system as areas needing constant monitoring. That paradigm has changed with the recognition that all areas of the water supply network are vulnerable to intentional contamination, most particularly the distribution system via a method known as backflow attack.
Backflow Attacks
A backflow attack occurs when a pump is used to overcome the pressure gradient that is present in the distribution system's pipes. The pressure gradient can be easily overcome by using pumps available for rent or purchase at most home improvement stores. After the pressure has been overcome and a contaminant introduced, Bernoulli effects pull the contaminant into the flowing system and the normal movement of water in the system acts to disseminate the contaminant throughout the network affecting areas surrounding the introduction point.
The introduction point can be anywhere in the system. Studies conducted by the US Air Force and Colorado State University have shown this to be a very effective means of contaminating a system.
A few gallons of highly toxic material is enough, if injected at a strategic location via continuous feed, to contaminate an entire system supplying a population of 150,000 people in a matter of a few hours. According to Allman (see references), a terrorist could launch such an attack and be on a plane out of the country before the first casualties begin to show up.
Terrorists have definitely shown an interest in this sort of attack. On February 20, 2002 the Associated Press released a story with the following headline: "Four arrested with cyanide and Rome water supply maps." The article detailed a raid on an apartment and the arrest of four Moroccan terrorists. They were part of the Salafist Group for Call and Combat, an Algerian organisation with ties to Ossama bin Laden and the al Qaeda network.
According to the article, they were in possession of a common cyanide based industrial chemical later identified as Potassium Ferricyanide, false documents, and detailed maps of the area surrounding the US Embassy. Maps found in the apartment included details of the city's water system and the U.S. Embassy was circled on the maps. Investigators believed the suspects planned to contaminate the water supplies in the capital, including the commercial area around Via Veneto where the U.S. Embassy is located (BBC News 2002).
The solution
In the past several years, the recognition of these vulnerabilities has lead to the rapid development of analytical techniques and instrumentation packages designed to address the monitoring needs of the new security based paradigm. A number of studies, conducted since 9/11, have shown that one of the key techniques capable of addressing the need to be vigilant in all sections of the water supply network is bulk parameter monitoring of basic water quality parameters, coupled with interpretive algorithms.
These studies have shown the utilisation of multi–parameter monitoring has the potential to indicate the presence of a wide variety of harmful agents in water at levels that would be protective of human health (Hall et. al 2007, Kroll 2006, USEPA 2005).
One such unit (The Hach GuardianBlue System) makes use of five common bulk parameters that are monitored simultaneously in real time. The parameters that are monitored are pH, Conductivity, Total Organic Carbon, Turbidity and Residual Chlorine.
As the system is designed, the signals from all of the instruments are processed from five separate parameter measures into a single value in an event monitor computer system. This contains a number of algorithms. The signal then goes through the crucial proprietary baseline estimator. A deviation of the signal from the estimated baseline is then derived. A gain matrix is then applied that weights the various parameters based on experimental data for a wide variety of probable threat agents.
The magnitude of the deviation signal is then compared to a preset threshold level that is set by the operator. If the signal exceeds the threshold, the trigger is activated. This makes interpretation of the huge amounts of data generated by such instrument packages streamlined and easy for operators to interpret.
These systems appear to be a good choice for detecting water quality excursions that could be linked to water security events. There are a number of advantages to using such systems. The chief advantage is that these instruments are not new – they are common everyday parameters with which the average industry worker is quite familiar, thus adding a degree of comfort in operations not afforded by other new technology. As existing technologies, these instruments have been proven to be robust and dependable in prior field deployments. They represent measurements that would be of interest and use to water utility personnel above and beyond their role as water security devices.
Deployments around the world
The system described has been in use throughout the United States for a number of years. Here it has achieved the US Department of Homeland Security's designation as a certified anti–terrorism device under the SAFETY Act. Such success in the US has led to its adoption at a number of locations throughout the world to enhance the security of the distribution systems, including Israel and China.
In China the system was deployed during the Beijing Olympics where it played an invaluable part in securing the Olympic venues and athletes for a potential terrorist attack on their water supplies. Other countries such as Canada and Singapore have deployed systems not simply under the auspices of water security programs but also for general water quality monitoring. This dual use capability of the system for general water quality surveillance makes the concept even more valuable. The system is able to alert and, in many cases, classify the most likely potential cause whenever a significant deviation in water quality is detected.
These sensors have been instrumental in detecting a number of occurrences that would have gone unnoticed without monitoring. These sort of observations include road work events, pressure problems, rain events, variable demand problems, ammonia overfeeds, chlorine feed problems including over and underfeeds, fluoride overfeeds, bad check valves, flushing problems, inaccurate grab sampling programs, un–calibrated hydraulic models, and main breaks among others (Kroll et. al. 2009).
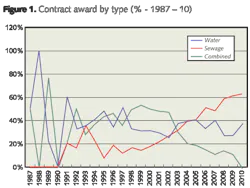
One interesting event that was detected by such a system was an overfeed of caustic that if not detected could have resulted in serious injury. In this deployment scenario, the plant used caustic feed to control water pH. The system experienced a trigger that when investigated was identified as an operational problem that resulted in the feed of excess caustic. The result was that the overfeed affected the pH and the conductivity of the water, causing the alarm (See figure 1).
The reason behind this was that the vendor from which the caustic was being purchased had delivered the wrong concentration of the solution. No–one had checked to see if the concentration was correct before feeding in the material. New procedures were put in place to verify incoming raw materials. The Event Monitor learned this Plant Event and was able to classify a recurrence of the event in the future, incase a there is a repeat of a failure in the system.
Another good example of dual use occurred when a municipality that had recently installed such a system was faced with a disgruntled customer. The customer, a major industrial user of the city's water supply, was complaining about poor quality water that was adversely affecting their processes and, they threatened legal action.
Fortunately, a multi–parameter security system had been installed near the facility and had recorded data on water quality during the time frame of the dispute. After reviewing the data with the customer, the city helped the customer locate the source of the actual problem, which turned out to be the recirculation loop within the plant, thus saving the city the potential costs of a court battle.
Early detection
Monitoring is a critical component of any water security/quality program. There is no other feasible way to address the severe vulnerability of an intentional contamination event, especially in the distribution system. The early detection of such an event is imperative if there is to be any hope of decreasing casualties and limiting damage to infrastructure.
With the current state of on–line monitoring there is no need for us to remain blind to the changes in water quality that can occur once the water has left the treatment plant. Whether it is detecting terrorist activity, accidental contamination or the everyday problems that can occur in any distribution system, an on–line monitoring system is an indispensible ingredient in the recipe for maintaining the quality of water from source to tap.
References
Allman. Timothy. 2003. Drinking water distribution system modeling for predicting the impact and detection of intentional contamination, Masters Thesis, Colorado State University, Dept of Engineering, Fort Collins Colorado, Summer
BBC News. 2002 "Cyanide attack foiled in Italy" Wednesday, 20 February 2002, http://news.bbc.co.uk/1/hi/world/europe/1831511.stm
EPA. 2005. "Multi–parameter Water Monitors for Distribution Systems". A series of EPA Environmental Technology Verification reports performed by Battelle. http://www.battelle.org/PRODUCTSCONTRACTS/etv/verifications.aspx#W12
Hall, John et al. 2007. "On–line Water Quality Parameters as Indicators of distribution System Contamination." Journal of the American Water Works Association. Vol. 99 Issue 1.
Kroll, Dan. 2006. "Safeguarding the Distribution System: On–Line Monitoring for Security and Enhancing Operational Performance" Journal of the New England Water Works Association. June 2006.
Kroll et. al. 2009. Let's get real. Real world experiences with real time on–line monitoring for security and quality. Detecting and responding to events. A Chapter in the book "Water Contamination Emergencies. Collective Responsibility." Edited by John Gray and Clive Thompson. Royal Society of Chemistry. Cambridge, UK.
Author's note: Dan Kroll is the chief scientist at Hach Homeland Security Technologies.
More Water & WasteWater International Current Issue Articles
More Water & WasteWater International Archives Issue Articles